

Serverless architecture
Manual resource deployment and setup guide
November 2021
Information in this document, including URL and other Internet Web site references, is subject to change without notice. Unless otherwise noted, the example companies, organizations, products, domain names, e-mail addresses, logos, people, places, and events depicted herein are fictitious, and no association with any real company, organization, product, domain name, e-mail address, logo, person, place or event is intended or should be inferred. Complying with all applicable copyright laws is the responsibility of the user. Without limiting the rights under copyright, no part of this document may be reproduced, stored in or introduced into a retrieval system, or transmitted in any form or by any means (electronic, mechanical, photocopying, recording, or otherwise), or for any purpose, without the express written permission of Microsoft Corporation.
Microsoft may have patents, patent applications, trademarks, copyrights, or other intellectual property rights covering subject matter in this document. Except as expressly provided in any written license agreement from Microsoft, the furnishing of this document does not give you any license to these patents, trademarks, copyrights, or other intellectual property.
The names of manufacturers, products, or URLs are provided for informational purposes only and Microsoft makes no representations and warranties, either expressed, implied, or statutory, regarding these manufacturers or the use of the products with any Microsoft technologies. The inclusion of a manufacturer or product does not imply endorsement of Microsoft of the manufacturer or product. Links may be provided to third party sites. Such sites are not under the control of Microsoft and Microsoft is not responsible for the contents of any linked site or any link contained in a linked site, or any changes or updates to such sites. Microsoft is not responsible for webcasting or any other form of transmission received from any linked site. Microsoft is providing these links to you only as a convenience, and the inclusion of any link does not imply endorsement of Microsoft of the site or the products contained therein.
© 2021 Microsoft Corporation. All rights reserved.
Microsoft and the trademarks listed at https://www.microsoft.com/legal/intellectualproperty/Trademarks/Usage/General.aspx are trademarks of the Microsoft group of companies. All other trademarks are property of their respective owners.
Contents:
Duration: 30 minutes
This guide provides instructions for manually performing Task 2 (Run ARM template to provision lab resources) of the before the hands-on lab guide. The step-by-step directions below manually provision and configure the resources created by the ARM template.
Ensure all resources use the same resource group for easier cleanup.
Important: Many Azure resources require globally unique names. Throughout these steps, you will see the word “SUFFIX” as part of resource names. You should replace this with your Microsoft alias, initials, or other value to ensure uniquely named resources.
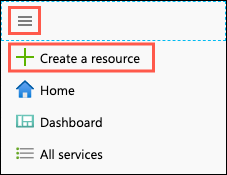
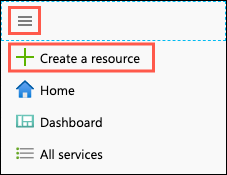
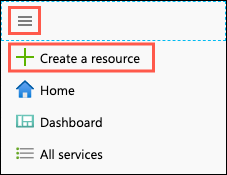
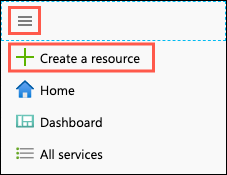
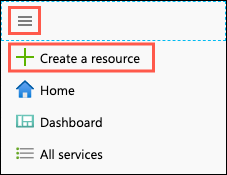
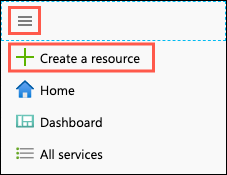
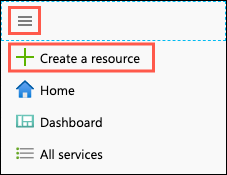
In the Azure portal, select the Show portal menu icon and then select +Create a resource from the menu.
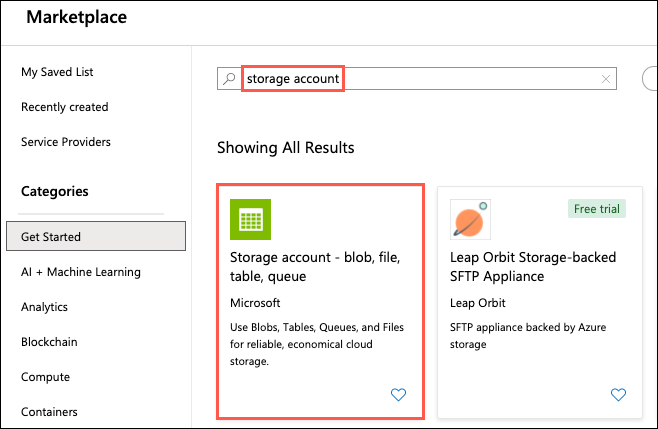
Enter “storage account” into the Search the Marketplace box, select Storage account from the results, and then select Create.
On the Create storage account Basics tab, enter the following:
Project Details:
Instance Details:
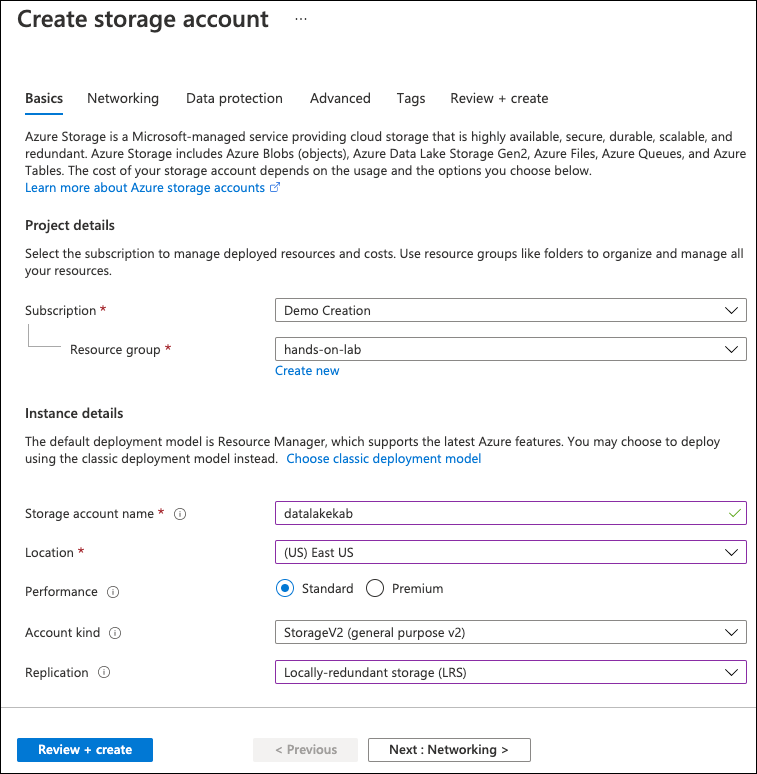
Next, select the Advanced tab.
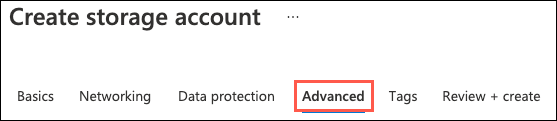
On the Advanced tab, select Enabled from the Hierarchical namespace setting under Data Lake Storage Gen2.
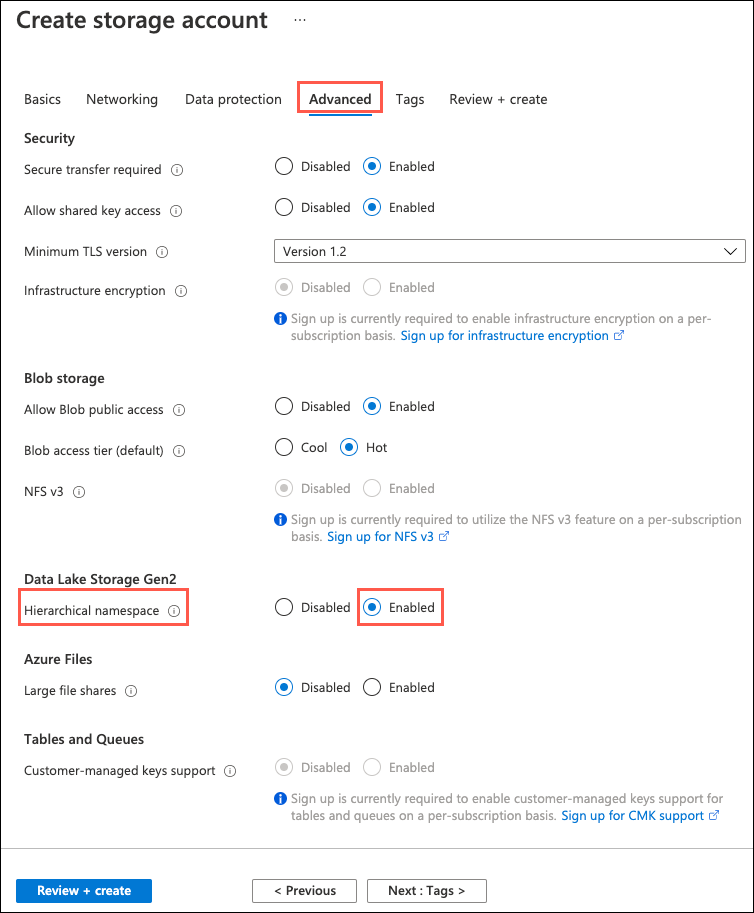
Select Review + create.
On the Review + create blade, ensure the Validation passed message is displayed and then select Create.
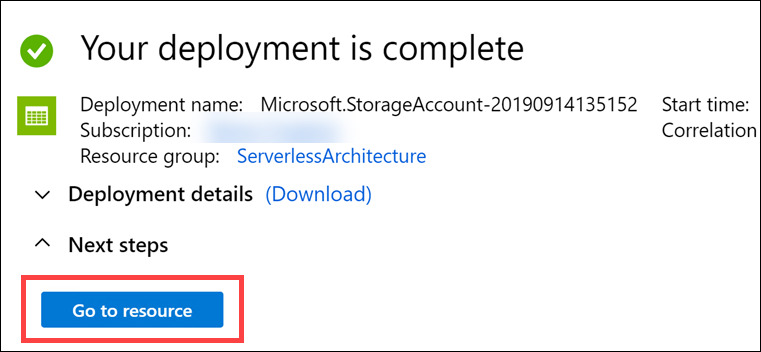
After the storage account has completed provisioning, open the storage account by selecting Go to resource.
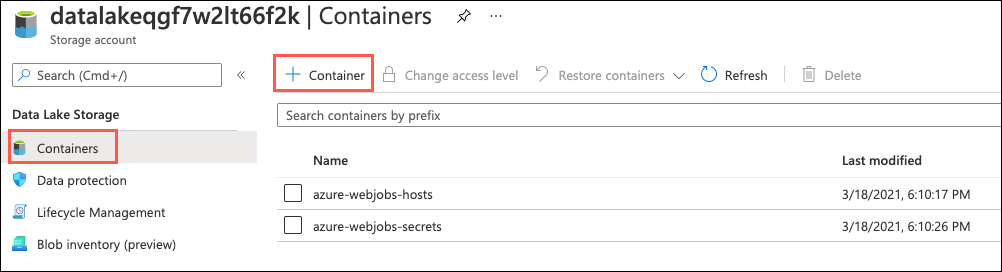
On the Storage account blade, select Containers under Data Lake Storage in the left-hand navigation menu and then select the + Container button to add a new container.
In the New container dialog, enter images into the Name field, choose Private (no anonymous access) for the public access level, then select Create to save the container.
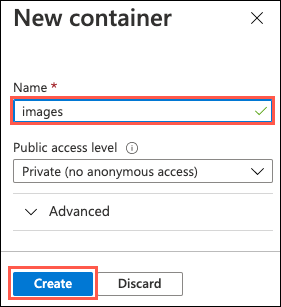
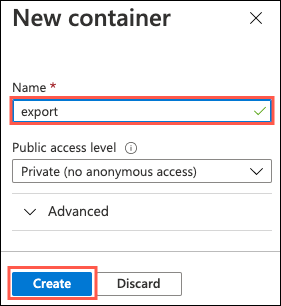
Repeat step 10 to create another container named export.
Next, select Access Keys, under Settings in the left-hand navigation menu. Then on the Access keys blade, select Show keys and then select the Click to copy button for the key1 connection string value.
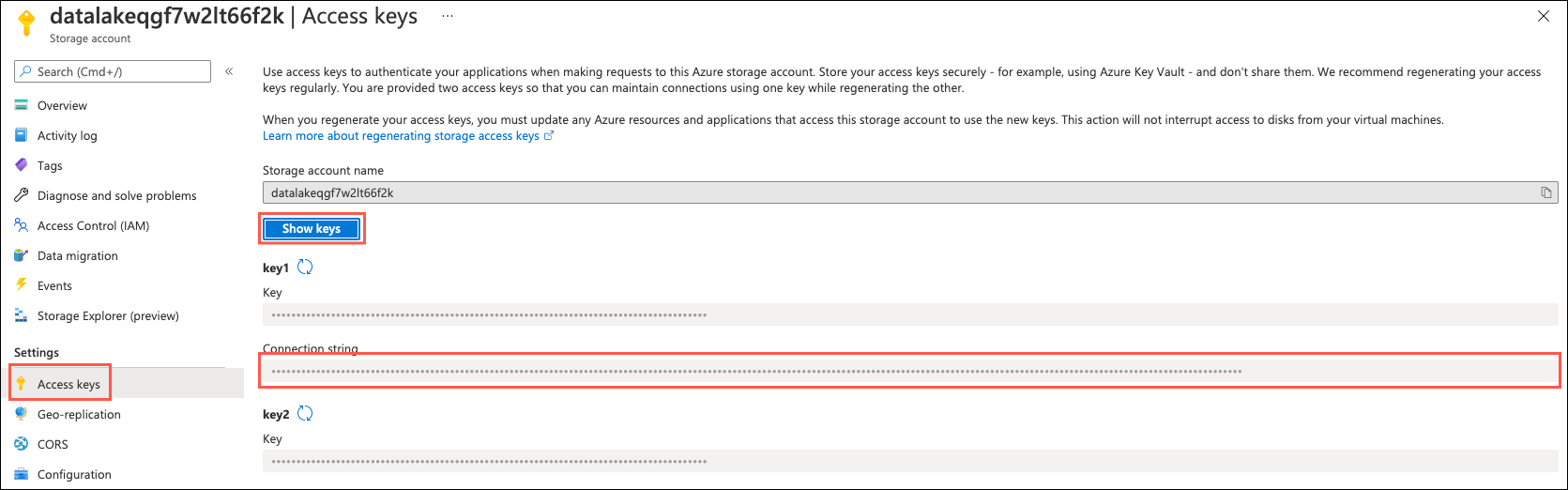
Paste the value into a text editor, such as Notepad, for reference in the Key Vault steps below.
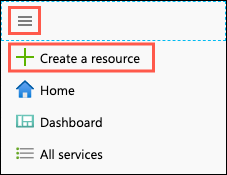
In the Azure portal, select the Show portal menu icon and then select +Create a resource from the menu.
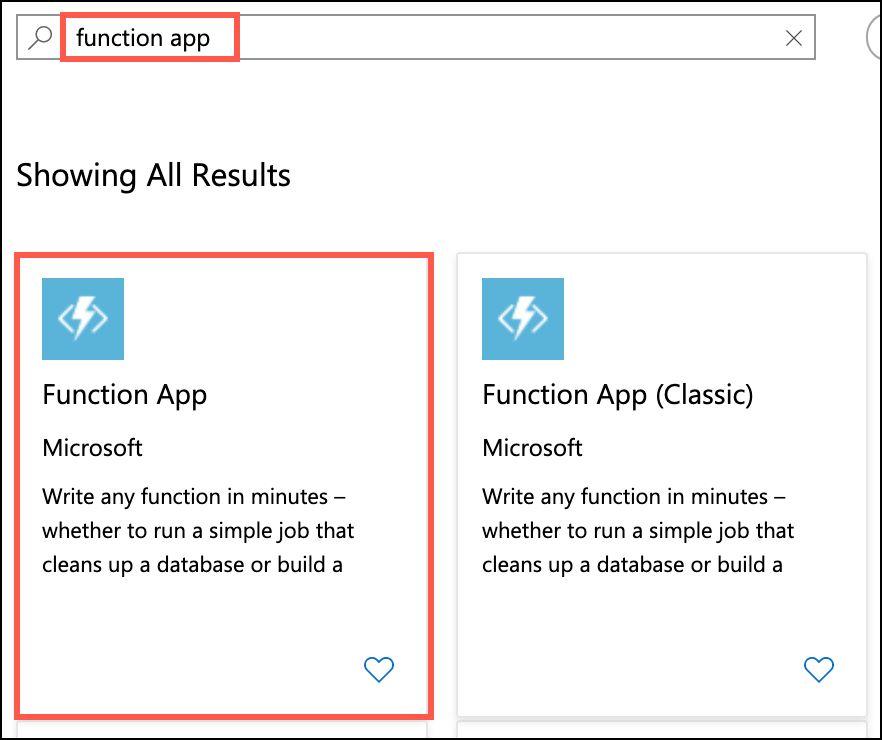
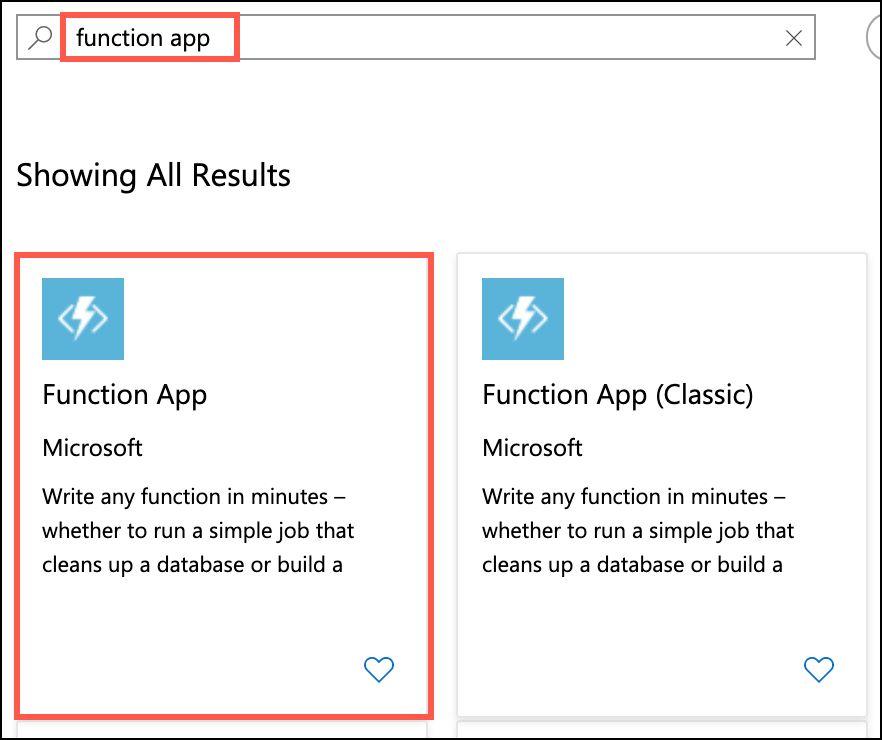
Enter “function app” into the Search the marketplace box and select Function App from the results.
On the Function App blade, select Create.
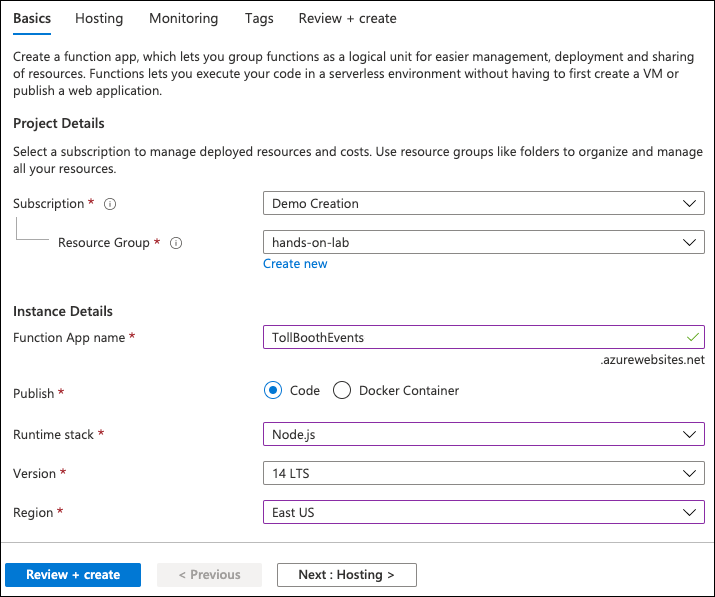
On the Create Function App blade, enter the following:
Project Details:
Instance Details:
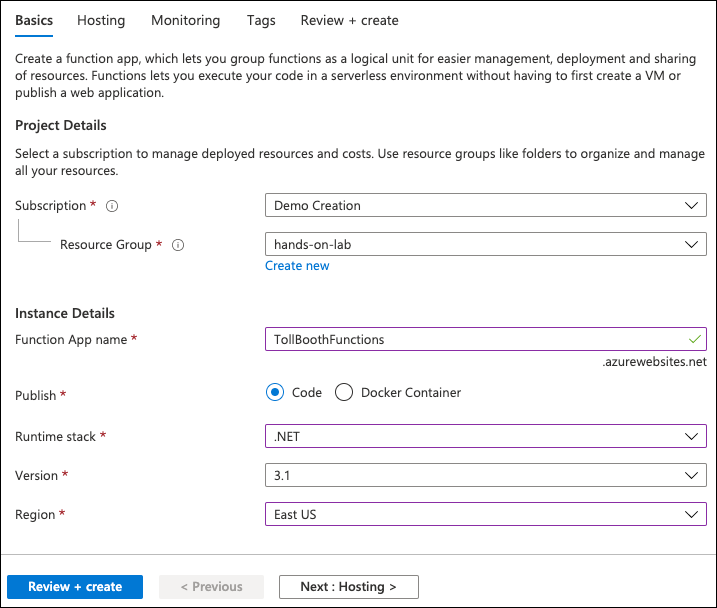
Select Next: Hosting.
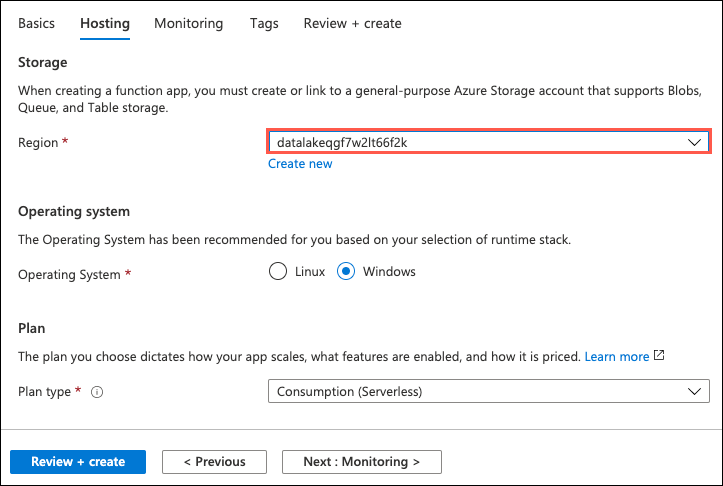
On the Hosting tab, set the following configuration:
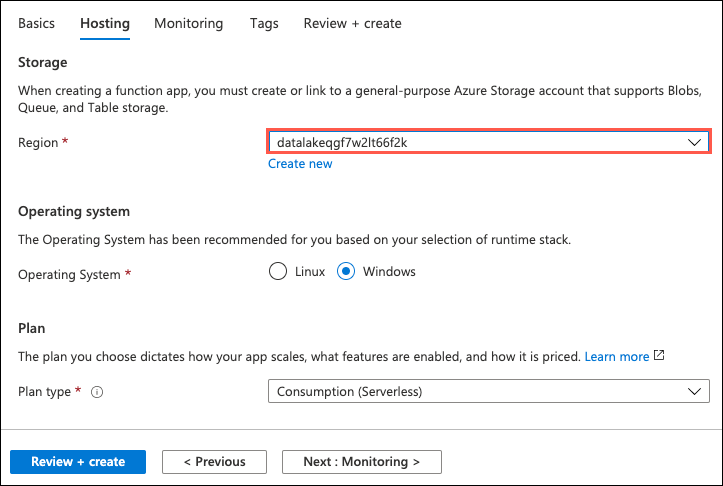
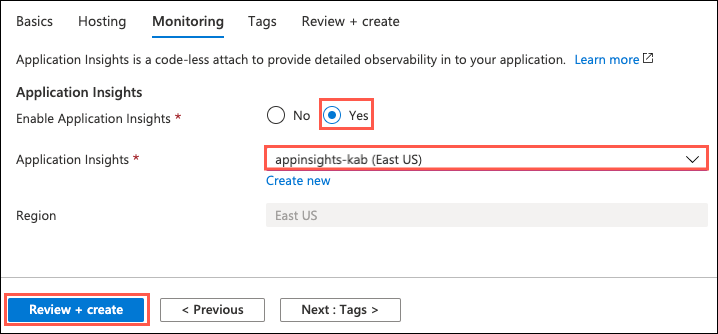
Select Next: Monitoring, and on the Monitoring tab, enter the following:
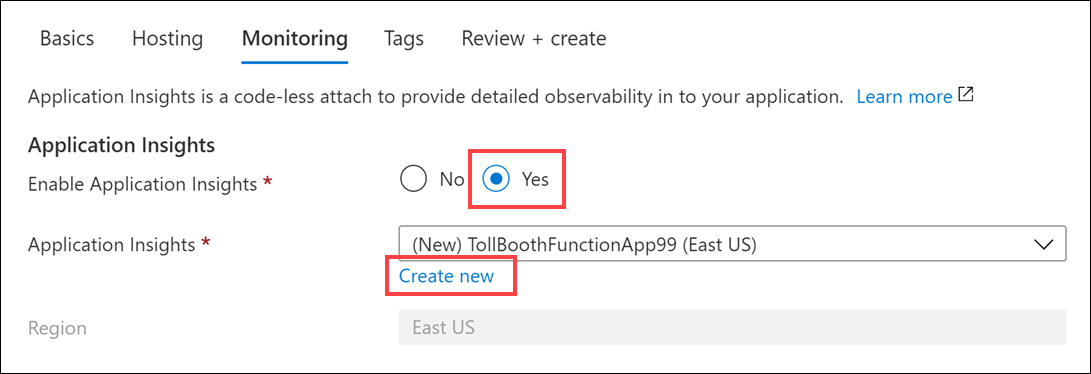
In the Create new Application Insights dialog, provide the following information, then select OK:

Select Review + create.

Select Create to provision the new Function App.
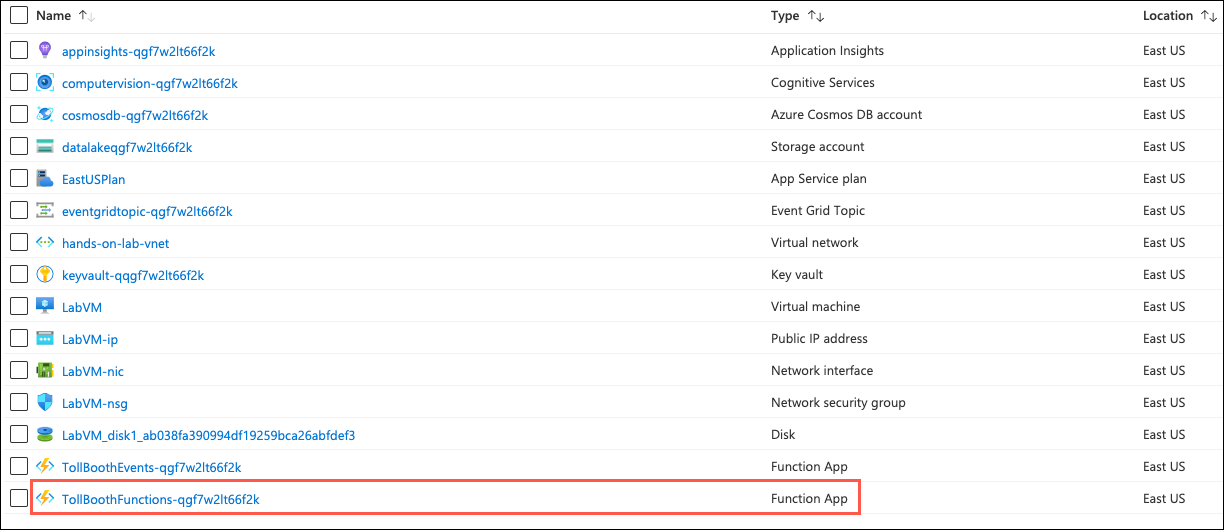
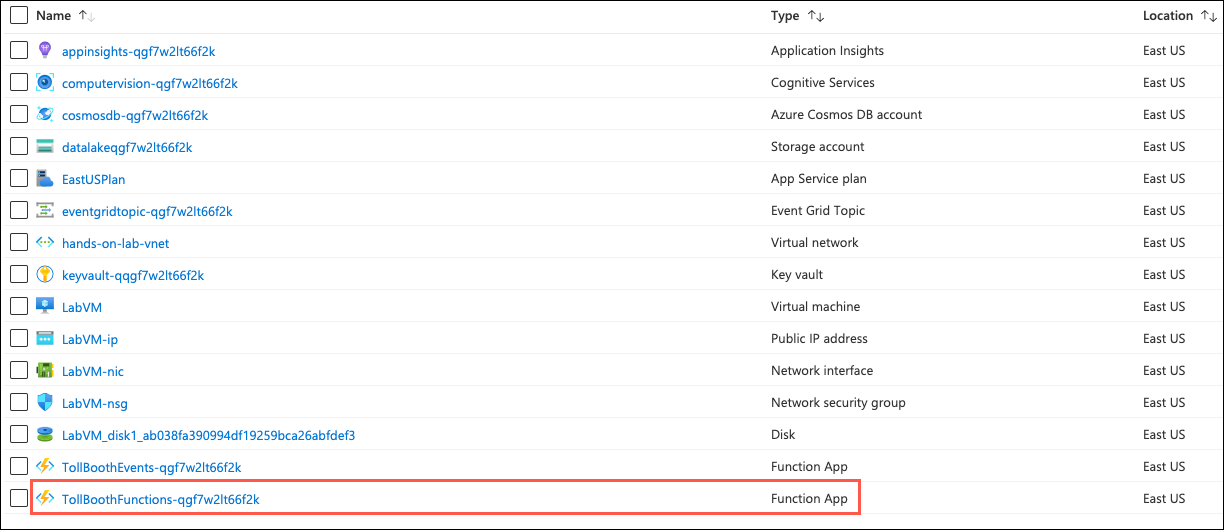
When the function app provisioning completes, navigate to it in the Azure portal by opening the hands-on-lab-SUFFIX resource group and then select the Azure Function App resource whose name begins with TollBoothFunctions.
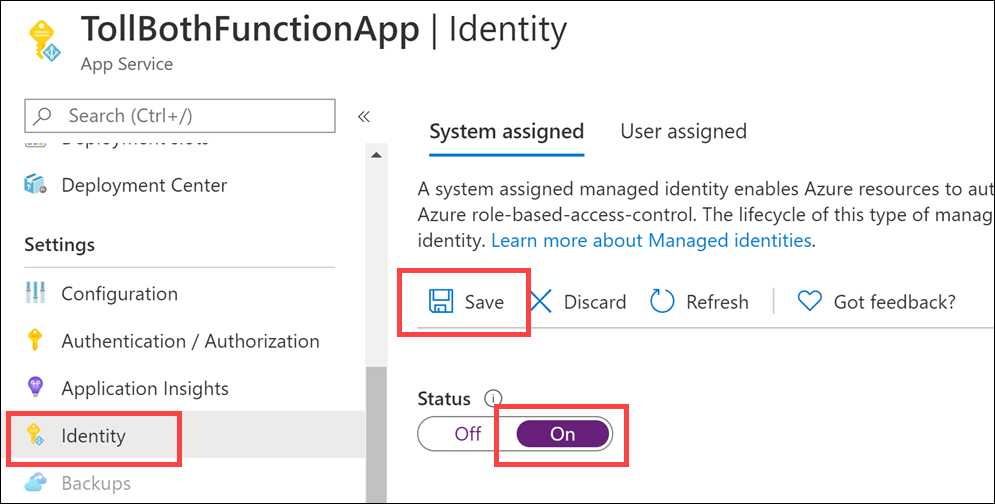
For your Function App to be able to access Key Vault to read the secrets, you must create a system-assigned managed identity for the Function App, and create an access policy in Key Vault for the application identity.
On the Function App blade, select Identity in the left-hand navigation menu, and within the System assigned tab, switch Status to On and select Save.
In the Azure portal, select the Show portal menu icon and then select +Create a resource from the menu.
Enter “function app” into the Search the marketplace box and select Function App from the results.
On the Function App blade, select Create.
On the Create Function App blade, enter the following:
Project Details:
Instance Details:
Select Next: Hosting.
On the Hosting tab, set the following configuration:
Select Next: Monitoring, and on the Monitoring tab, enter the following:
Select Review + create and then select Create to provision the Function App.
In the Azure portal, select the Show portal menu icon and then select +Create a resource from the menu.
Enter “event grid topic” into the Search the marketplace box and select Event Grid Topic from the results.
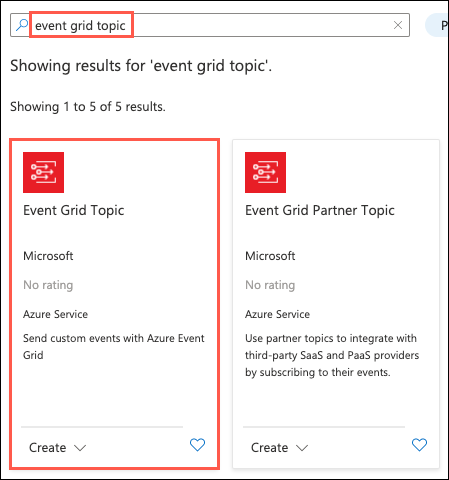
On the Event Grid Topic blade, select Create.
On the Create Topic blade, specify the following configuration options:
Project Details:
Instance Details:
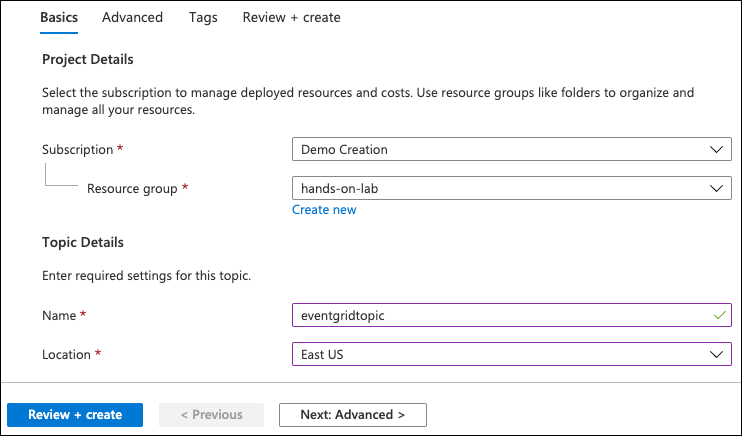
Select Review + Create, then select Create in the screen that follows.
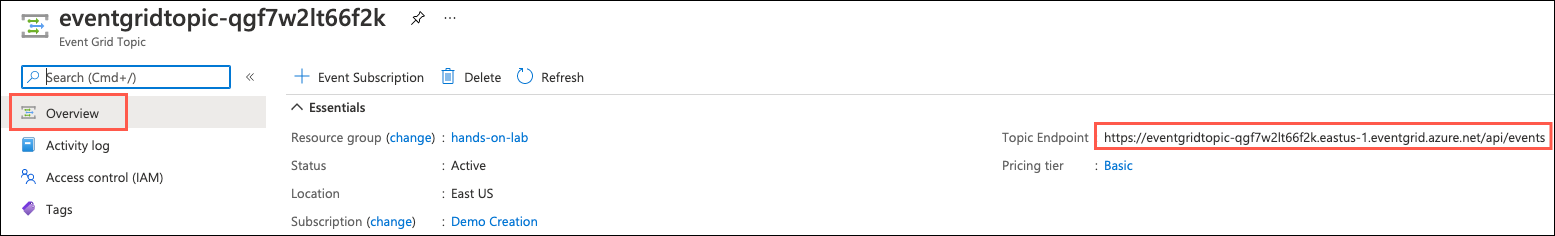
After the Event Grid topic has completed provisioning, open the account by opening the hands-on-lab-SUFFIX resource group and then selecting the Event Grid Topic resource from the list of available services.
On the Event Grid Topic blade, select Overview in the left-hand navigation menu and then copy the Topic Endpoint value and paste the value into a text editor, such as Notepad, for later reference.
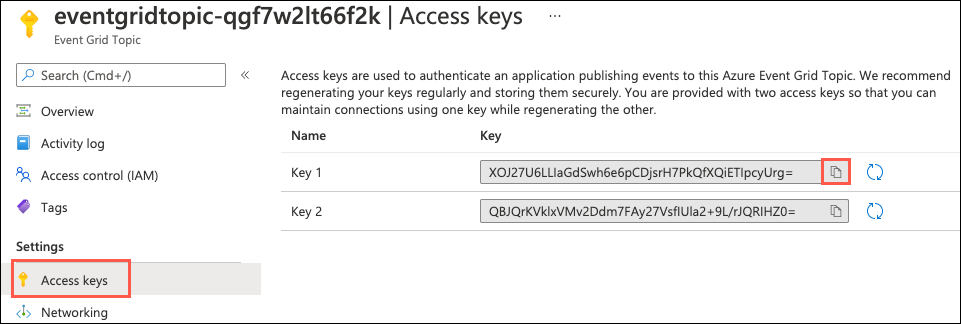
Next, select Access Keys under Settings in the left-hand navigation menu on the Event Grid Topic blade.
Within the Access Keys blade, copy the Key 1 value and paste it into a text editor, such as Notepad, for later reference.
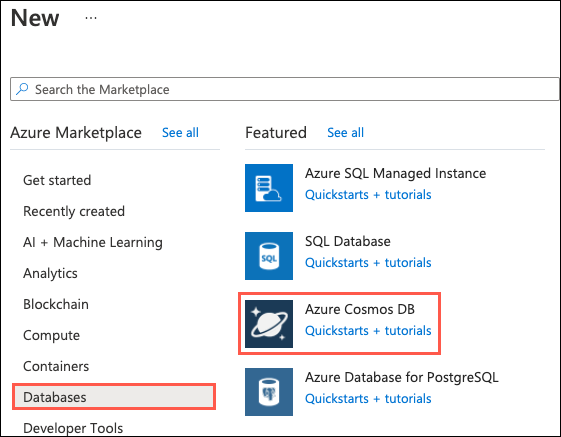
In the Azure portal, select the Show portal menu icon and then select +Create a resource from the menu.
On the New screen, select Databases then select Azure Cosmos DB.
On the Create new Azure Cosmos DB account blade, specify the following configuration options:
Project Details:
Instance Details:
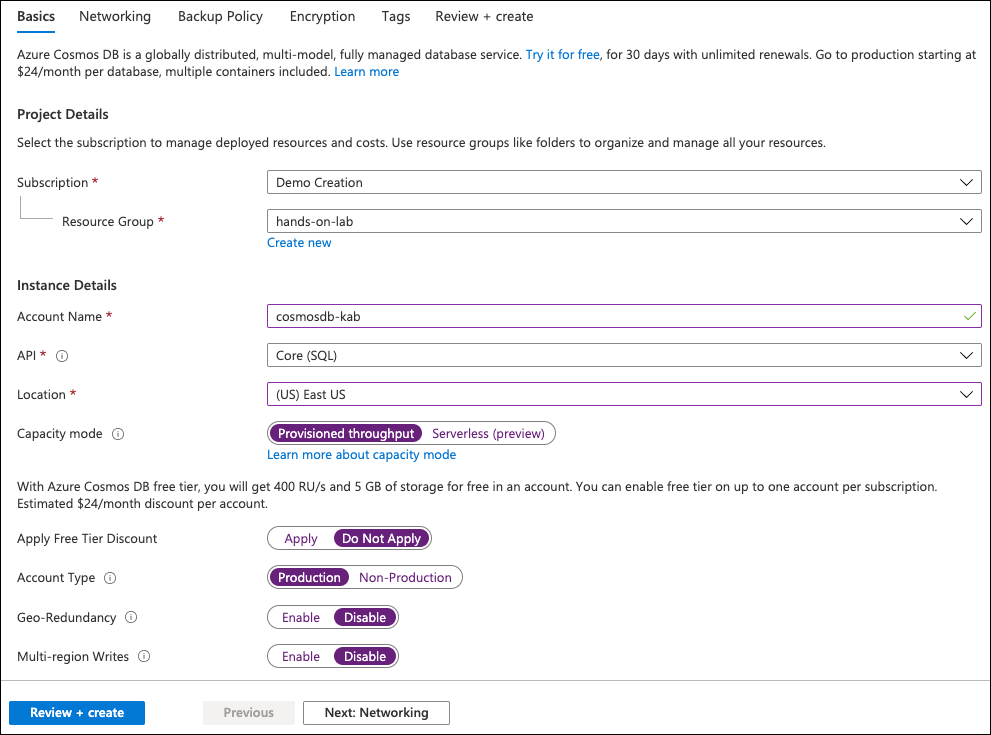
Select Review + create, then select Create.
After the Azure Cosmos DB account has completed provisioning, open the account by opening the hands-on-lab-SUFFIX resource group and then selecting the Azure Cosmos DB resource from the list of available services in the resource group.
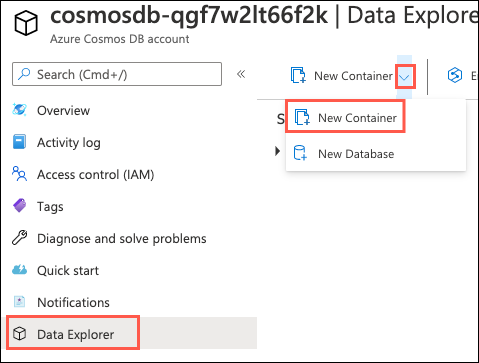
On the Cosmos DB blade, select Data Explorer in the left-hand navigation menu and then select New Container.
On the Add Container blade, specify the following configuration options:
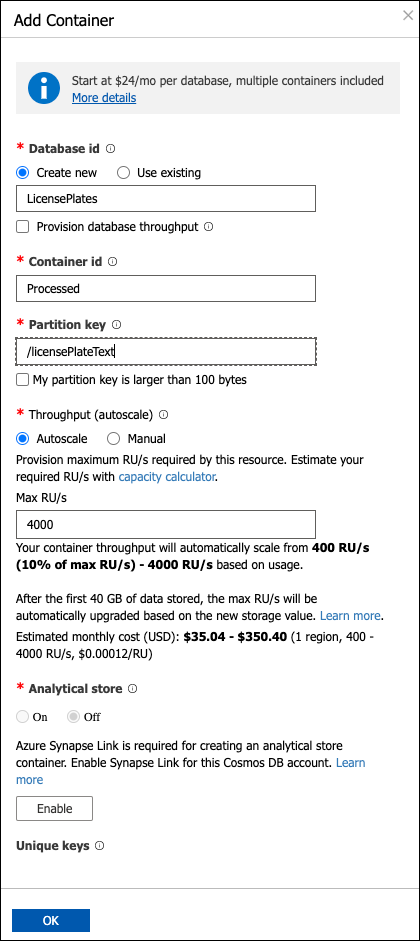
Select OK.
Select New Container again on the Data Explorer blade to add another container.
On the Add Container blade, specify the following configuration options:
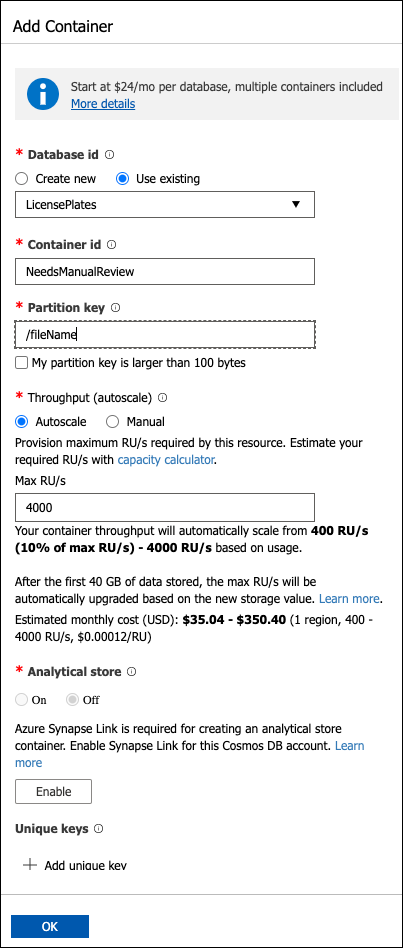
Select OK.
Select Keys under Settings in the left-hand navigation menu on the Cosmos DB blade.
Underneath the Read-write Keys tab within the Keys blade, copy the URI and Primary Key values.
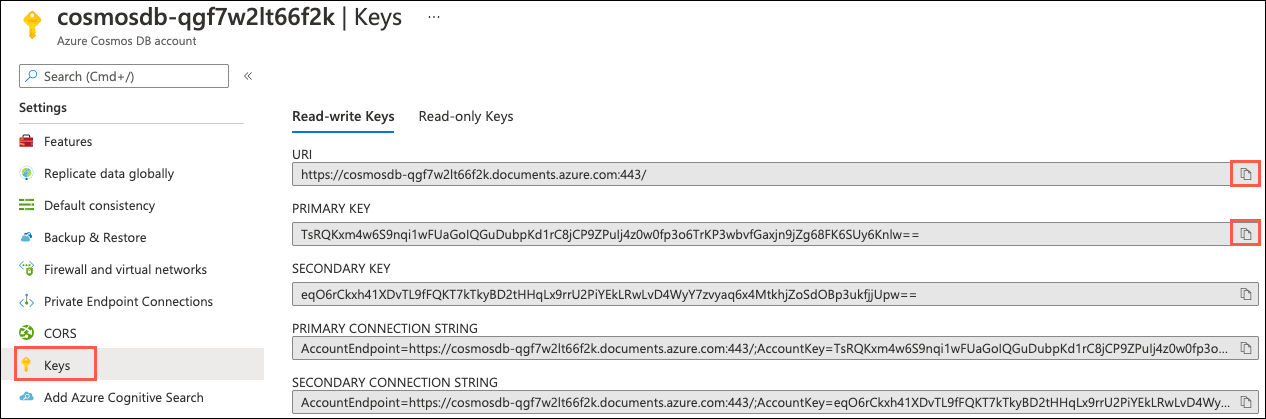
Paste the values into a text editor, such as Notepad, for later reference.
In the Azure portal, select the Show portal menu icon and then select +Create a resource from the menu.
Enter “computer vision” into the Search the marketplace box, select Computer Vision from the results, and then select the Create button on the Computer Vision blade.
On the Create Computer Vision blade, specify the following configuration options:
Project Details:
Instance Details:
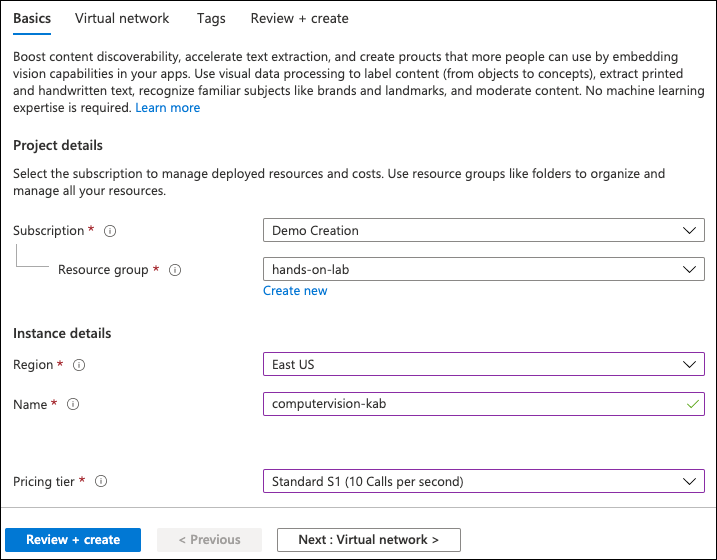
Select Review + create and then select Create.
After the Computer Vision service has completed provisioning, open the service by opening the hands-on-lab-SUFFIX resource group and then selecting the Computer Vision Cognitive Service resource from the list of available services in the resource group.
Under Resource Management in the left-hand navigation menu, select Keys and Endpoint.
Within the Keys and Endpoint blade, copy the Endpoint and KEY 1 values.
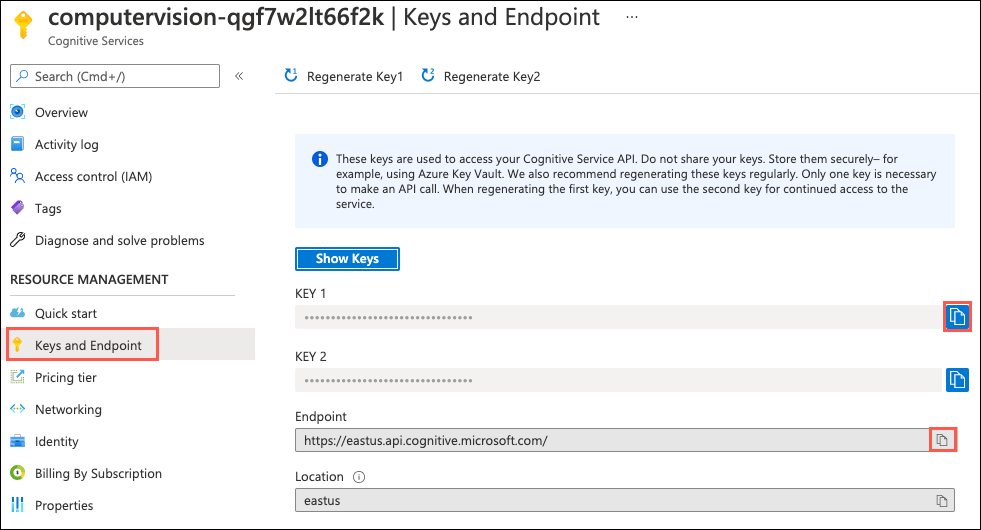
Paste the values into a text editor, such as Notepad, for later reference.
In the Azure portal, select the Show portal menu icon and then select +Create a resource from the menu.
Enter “logic app” into the Search the marketplace box and select Logic App from the results.
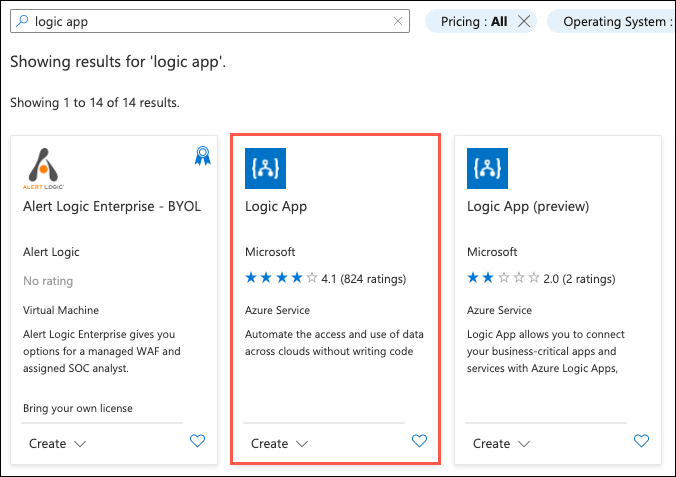
Select the Create button on the Logic App blade.
On the Create a logic app blade Basics tab, specify the following configuration options:
Project Details:
Instance Details:
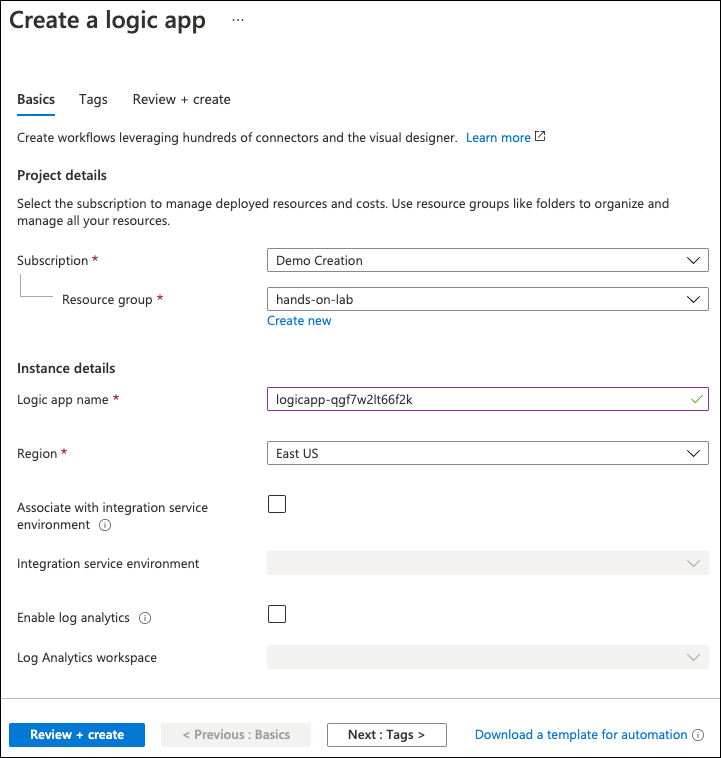
Select Review + create, then select Create.
In the Azure portal, select the Show portal menu icon and then select +Create a resource from the menu.
Enter “key vault” into the Search the marketplace box and select Key Vault from the results.
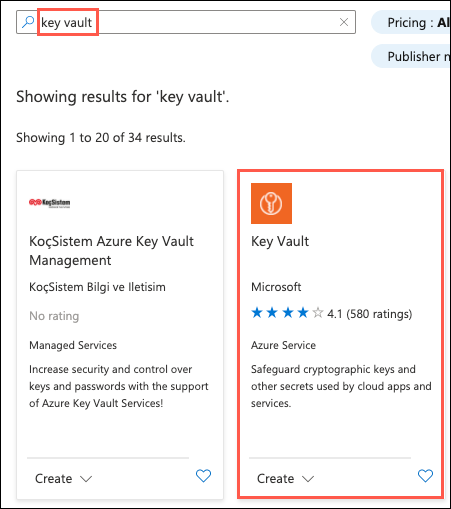
Select the Create button on the Key Vault blade.
On the Create key vault blade Basics tab, specify the following configuration options:
Project Details:
Instance Details:
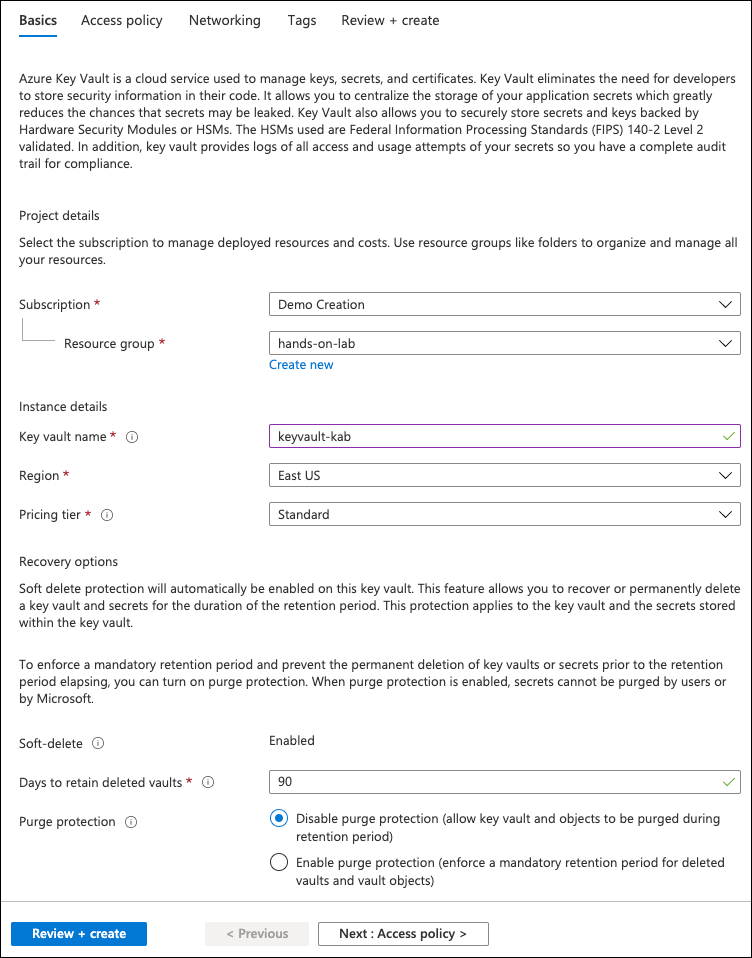
Select Next: Access policy.
On the Access policy tab, select Add Access Policy.
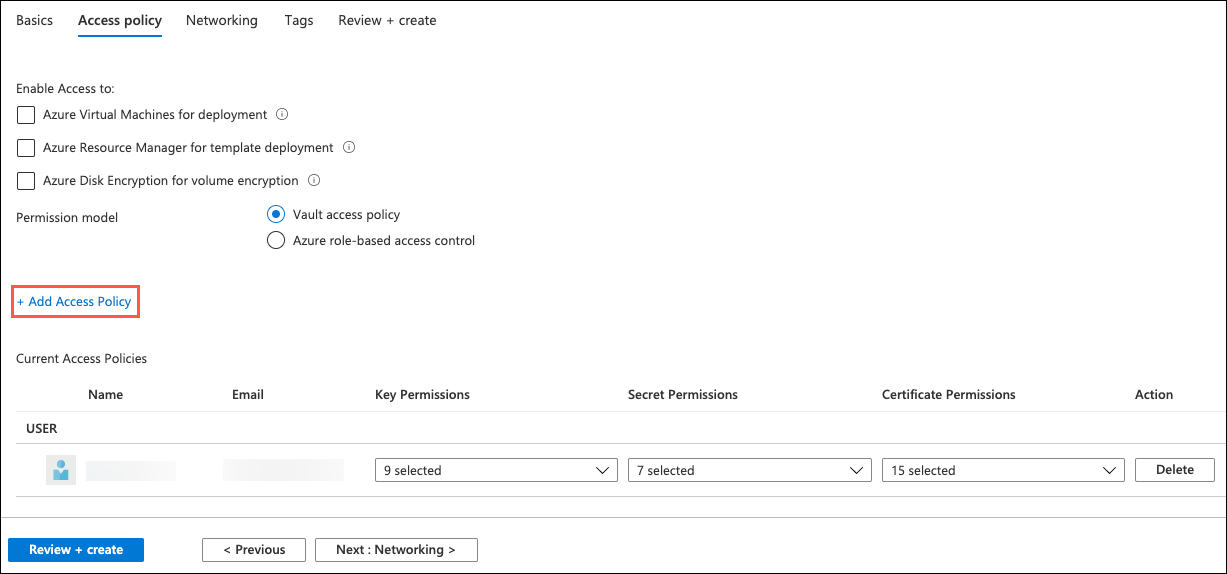
On the Add access policy dialog, enter the following:
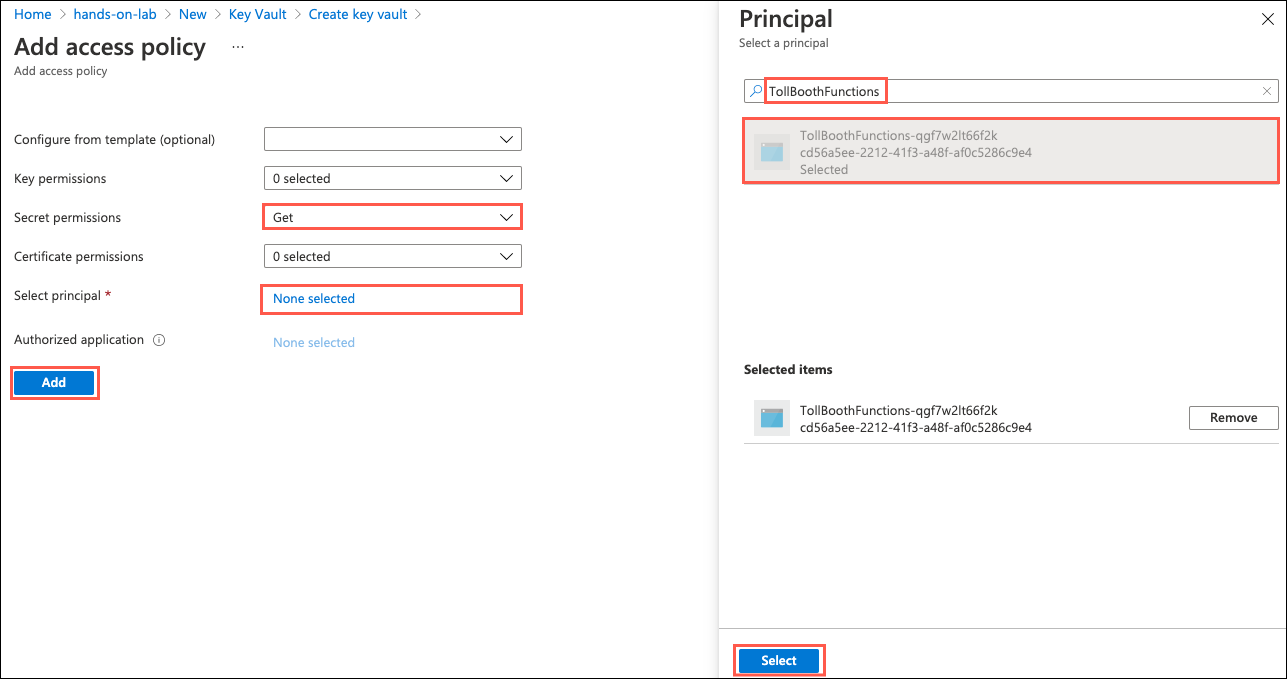
Select Add to add the new access policy.
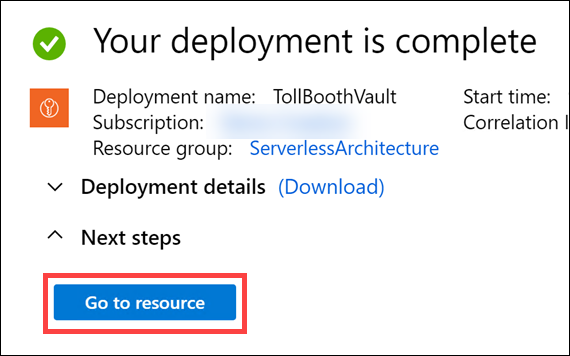
Select Review + create, then select Create.
After the deployment completes, select Go to resource in the deployment complete notification.
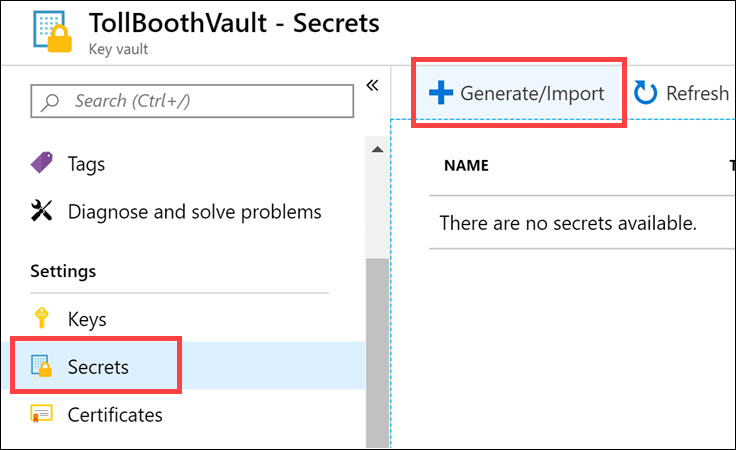
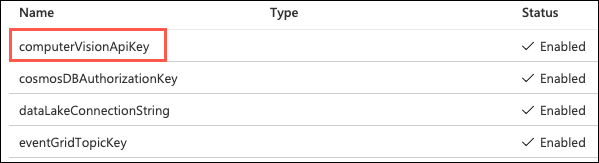
Select Secrets under Settings in the left-hand navigation menu.
Select Generate/Import to add a new key.
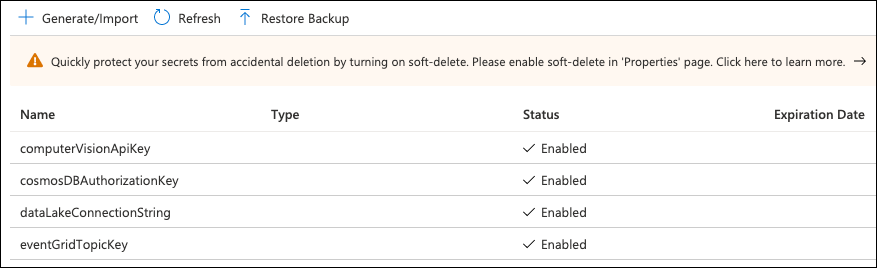
Using the key values you copied into a text editor, such as Notepad, in the tasks above, use the table below for the name-value pairs to use when creating the secrets. You only need to populate the Name and Value fields for each secret and leave the other fields at their default values.
| Name | Value |
| computerVisionApiKey | Computer Vision API key |
| cosmosDBAuthorizationKey | Cosmos DB Primary Key |
| dataLakeConnectionString | Data Lake storage connection string |
| eventGridTopicKey | Event Grid Topic access key |
When you are finished creating the secrets, your list should look similar to the following:
Open your Key Vault instance in the portal.
Still on the Secrets page in Key Vault, select the computerVisionApiKey secret.
On the computerVisionApiKey blade, select the Current Version of the secret.
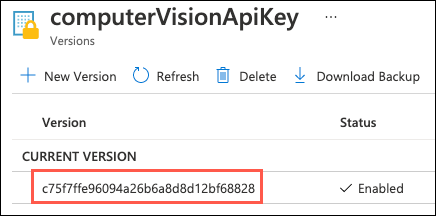
On the secret version blade, copy the Secret Identifier value by selecting the Copy to clipboard button.
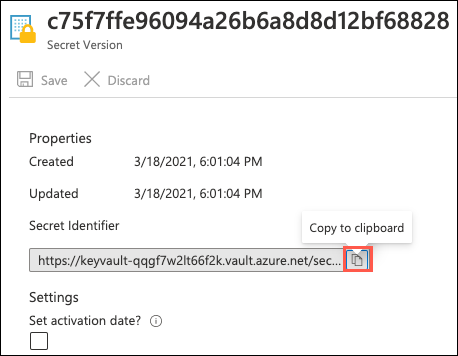
Paste the secret identifier value into a text editor, such as Notepad, for later reference.
Close the computerVisionApiKey blades and return to the Secrets page of your Key Vault.
Repeat steps 2 through 6 above for the other three secrets listed.
When you are done copying and pasting the secret identifier values, you should have a list similar to the following in your text editor document:
@Microsoft.KeyVault(SecretUri=https://tollboothvault.vault.azure.net/secrets/computerVisionApiKey/ce228a43f40140dd8a9ffb9a25d042ee)
@Microsoft.KeyVault(SecretUri=https://tollboothvault.vault.azure.net/secrets/cosmosDBAuthorizationKey/1f9a0d16ad22409b85970b3c794a218c)
@Microsoft.KeyVault(SecretUri=https://tollboothvault.vault.azure.net/secrets/dataLakeConnectionString/771aa40adac64af0b2aefbd741bd46ef)
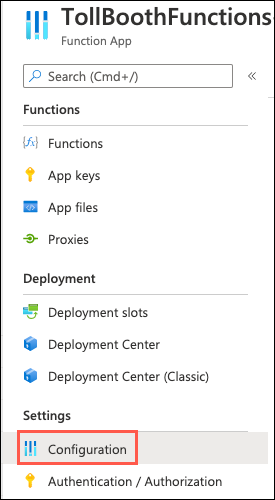
@Microsoft.KeyVault(SecretUri=https://tollboothvault.vault.azure.net/secrets/eventGridTopicKey/e310bcd71a72489f89b6112234fed815)Navigate to the TollBoothFunctions Function App resource in the Azure portal by opening the hands-on-lab-SUFFIX resource group and then select the Azure Function App resource whose name begins with TollBoothFunctions.
On the Function App blade, select Configuration in the left-hand navigation menu.
Scroll to the Application settings section. Use the + New application setting link to create the following additional key-value pairs (the key names must exactly match those found in the table below). Be sure to remove the curly braces ({}).
| Application Key | Value |
| computerVisionApiKey | Enter @Microsoft.KeyVault(SecretUri={referenceString}), where {referenceString} is the URI for the computerVisionApiKey Key Vault secret |
| computerVisionApiUrl | Computer Vision API endpoint you copied earlier with vision/v3.0/ocr appended to the end. Example: https://eastus.api.cognitive.microsoft.com/vision/v3.0/ocr |
| cosmosDBAuthorizationKey | Enter @Microsoft.KeyVault(SecretUri={referenceString}), where {referenceString} is the URI for the cosmosDBAuthorizationKey Key Vault secret |
| cosmosDBCollectionId | Cosmos DB processed collection id (Processed) |
| cosmosDBDatabaseId | Cosmos DB database id (LicensePlates) |
| cosmosDBEndpointUrl | Cosmos DB URI |
| dataLakeConnection | Enter @Microsoft.KeyVault(SecretUri={referenceString}), where {referenceString} is the URI for the dataLakeConnectionString Key Vault secret |
| eventGridTopicEndpoint | Event Grid Topic endpoint |
| eventGridTopicKey | Enter @Microsoft.KeyVault(SecretUri={referenceString}), where {referenceString} is the URI for the eventGridTopicKey Key Vault secret |
| exportCsvContainerName | Data lake CSV export container name (export) |
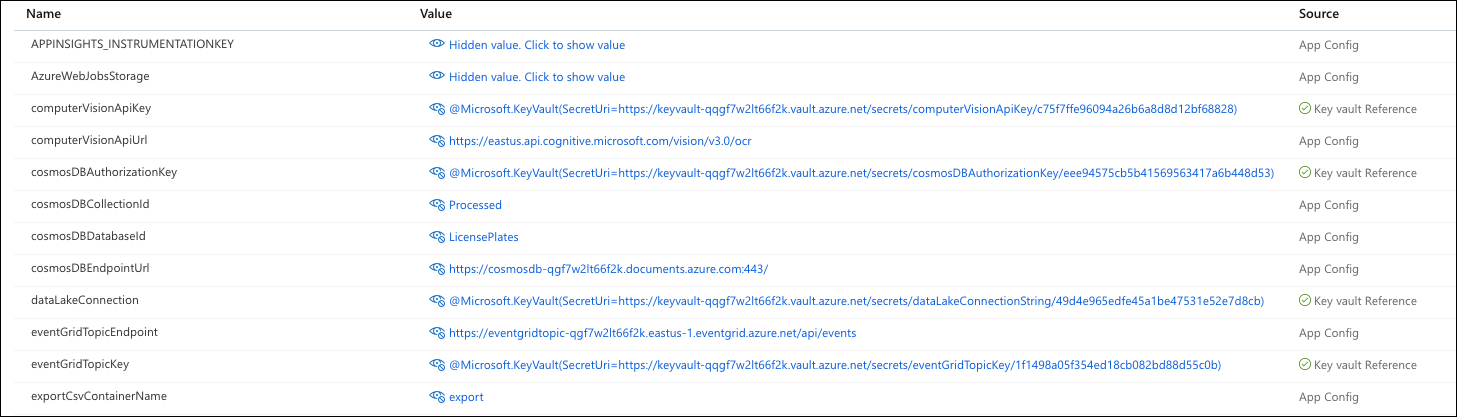
Select Save on the Configuration toolbar to save the application settings changes.
In this task, you provision a virtual machine (VM) in Azure. The VM image used has the latest version of Visual Studio Community 2019 installed.
In the Azure portal, select the Show portal menu icon and then select +Create a resource from the menu.
Enter “visual studio 2019” into the Search the Marketplace box and then select Visual Studio 2019 Latest from the results.
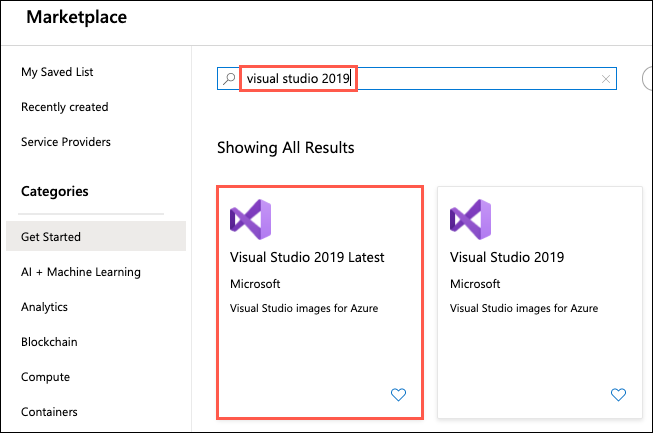
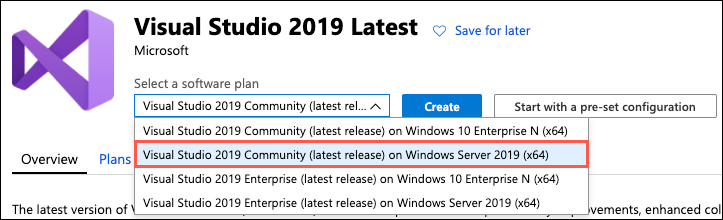
On the Visual Studio 2019 Latest blade, select Visual Studio 2019 Community (latest release) on Windows Server 2019 (x64) from the Select a software plan drop-down list, and then select Create.
On the Create a virtual machine Basics tab, set the following configuration:
Project Details:
Instance Details:
Administrator Account:
Inbound Port Rules:
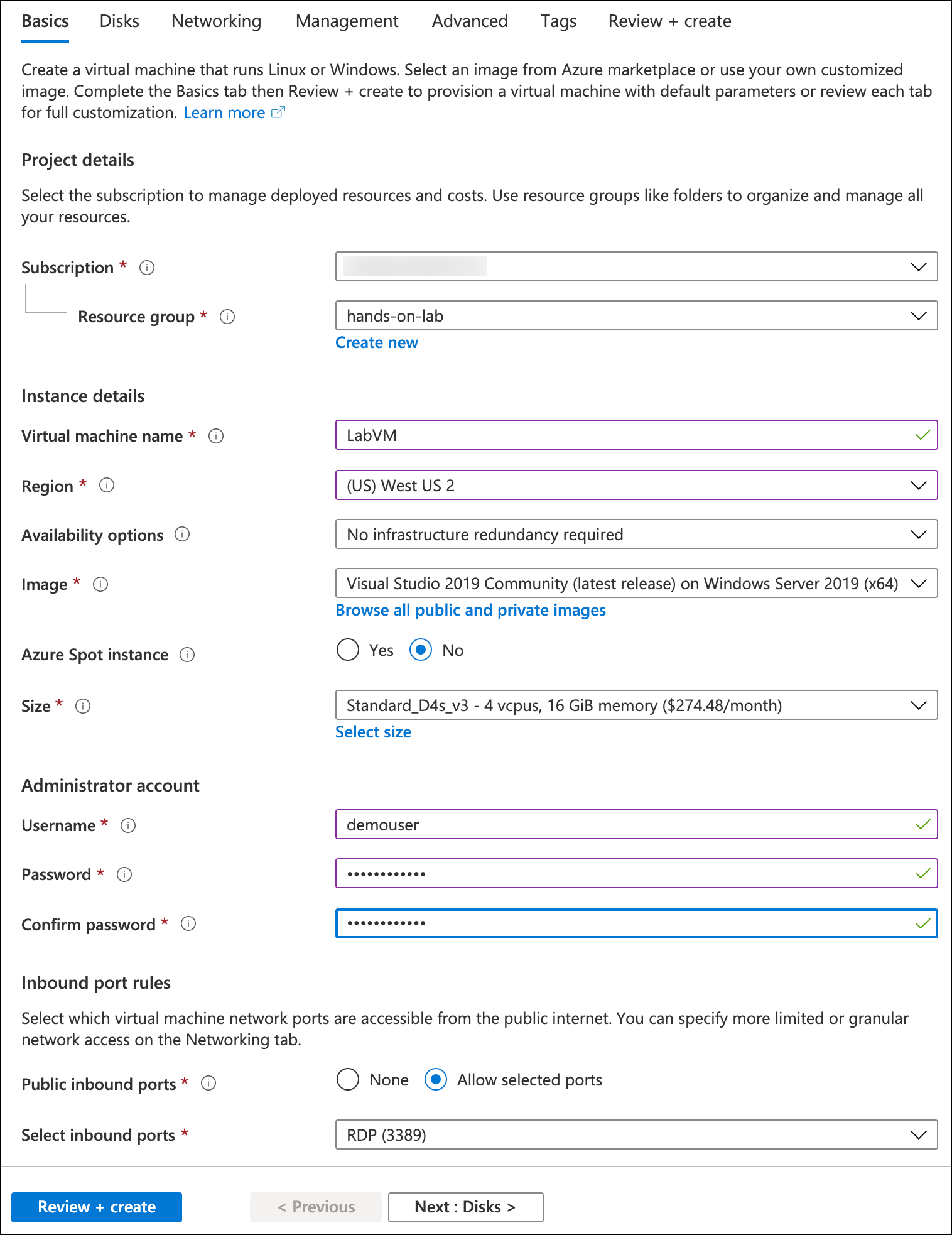
Note: Default settings are used for the remaining tabs so that they can be skipped.
Select Review + create to validate the configuration.
On the Review + create tab, ensure the Validation passed message is displayed, and then select Create to provision the virtual machine.
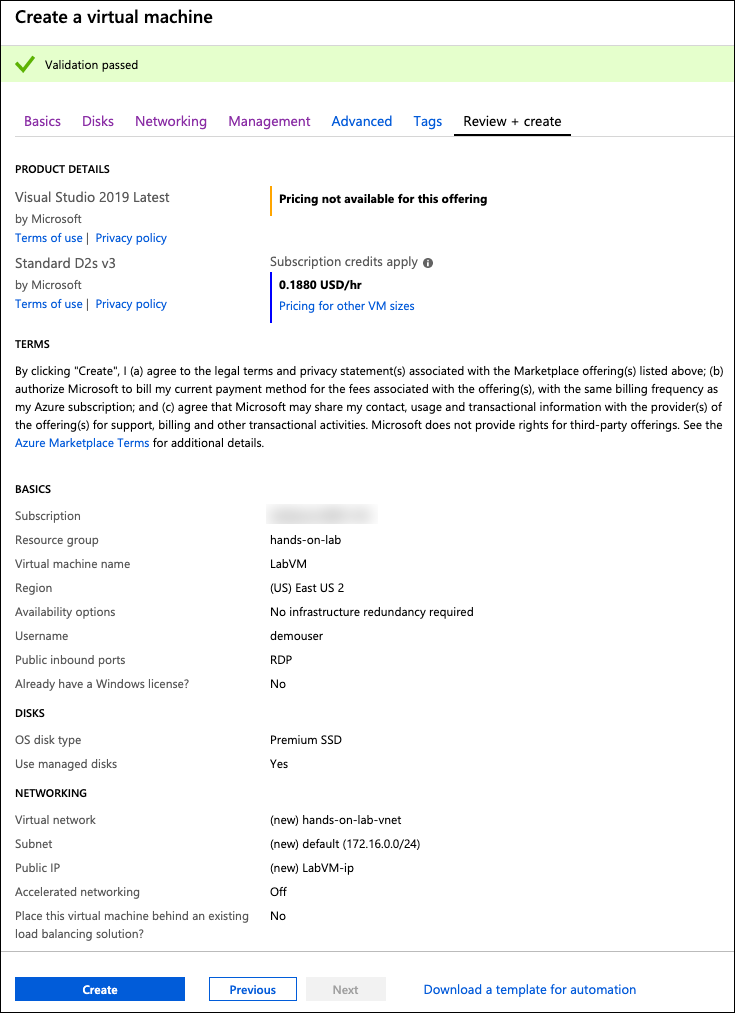
It takes approximately 5 minutes for the VM to finish provisioning.
In this task, you create an RDP connection to your Lab virtual machine (VM).
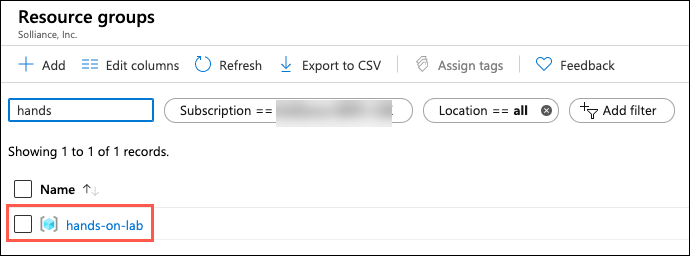
In the Azure portal, select Resource groups from the Azure services list.
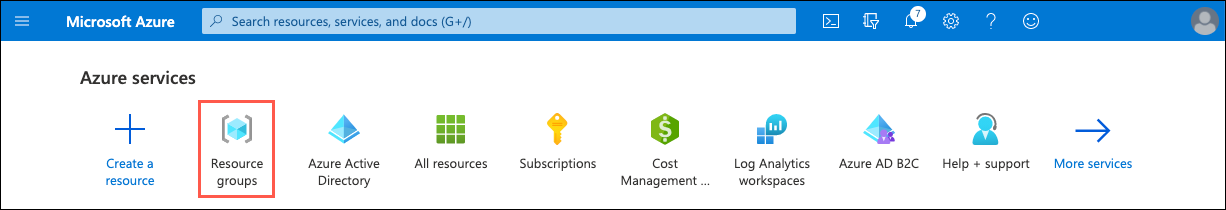
Select the hands-on-lab-SUFFIX resource group from the list.
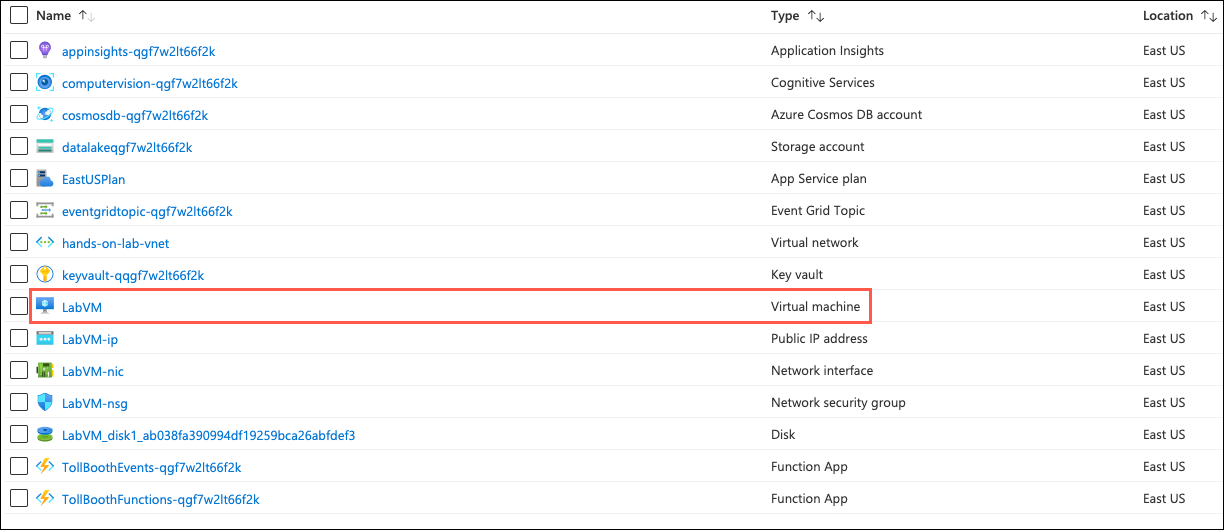
In the list of resources within your resource group, select the LabVM Virtual machine resource.
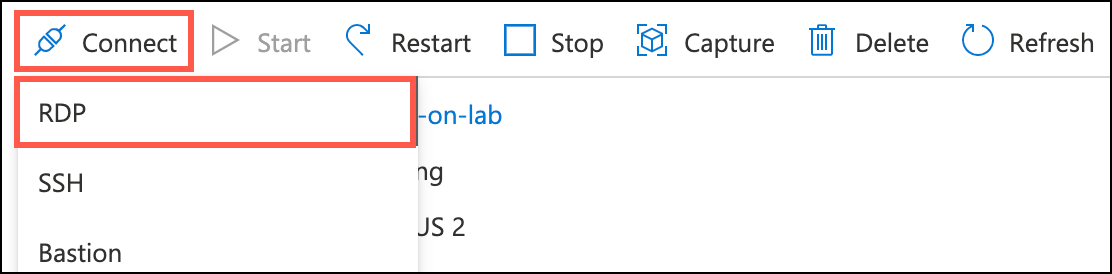
On your LabVM blade, select Connect and RDP from the top menu.
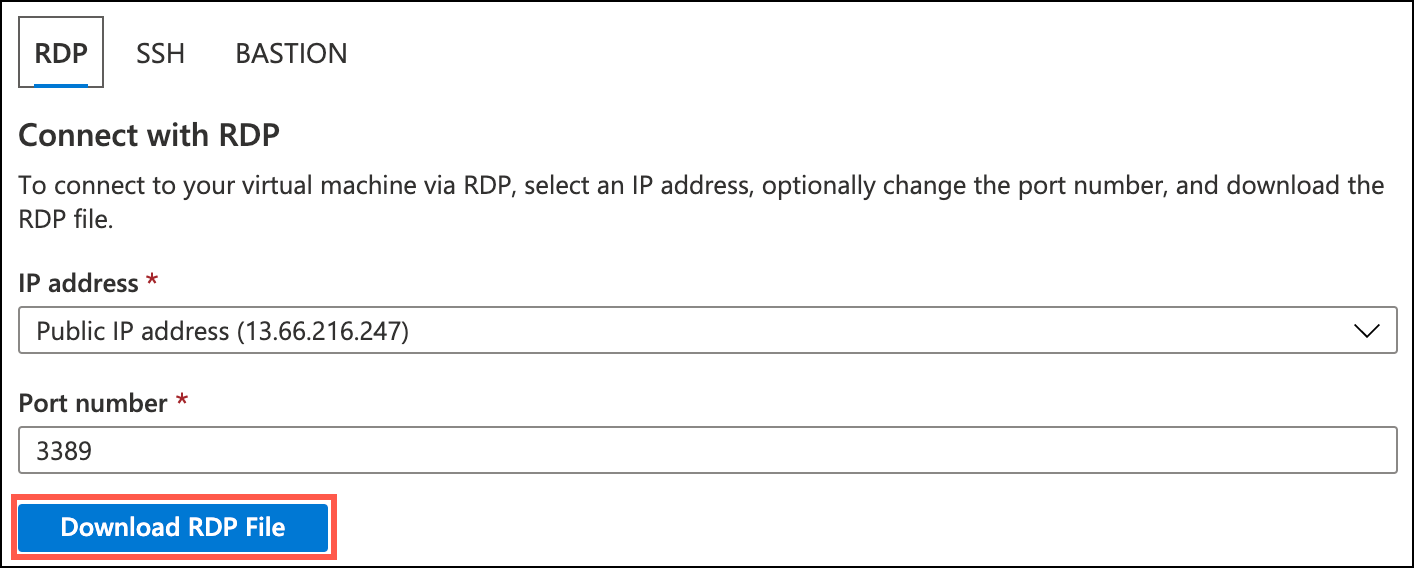
On the Connect to virtual machine blade, select Download RDP File, then open the downloaded RDP file.
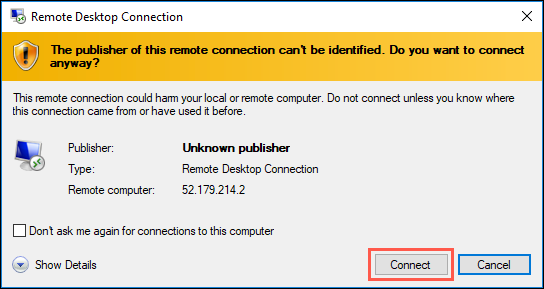
Select Connect on the Remote Desktop Connection dialog.
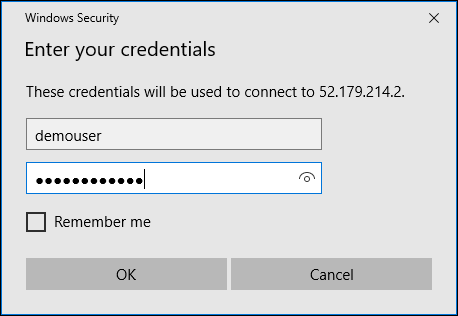
Enter the following credentials when prompted, and then select OK:
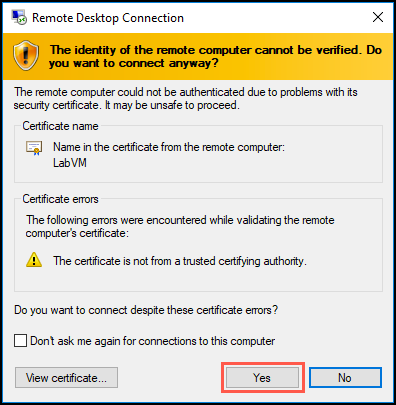
Select Yes to connect if prompted that the remote computer’s identity cannot be verified.
In this task, you disable Internet Explorer Enhanced Security Configuration (IE ESC) on the LabVM.
Note: Sometimes this Visual Studio 2019 Latest image has IE ESC disabled already, and sometimes it does not.
Once logged in, launch the Server Manager. This should start automatically, but you can access it via the Start menu if it does not.
Select Local Server, then select On next to IE Enhanced Security Configuration.
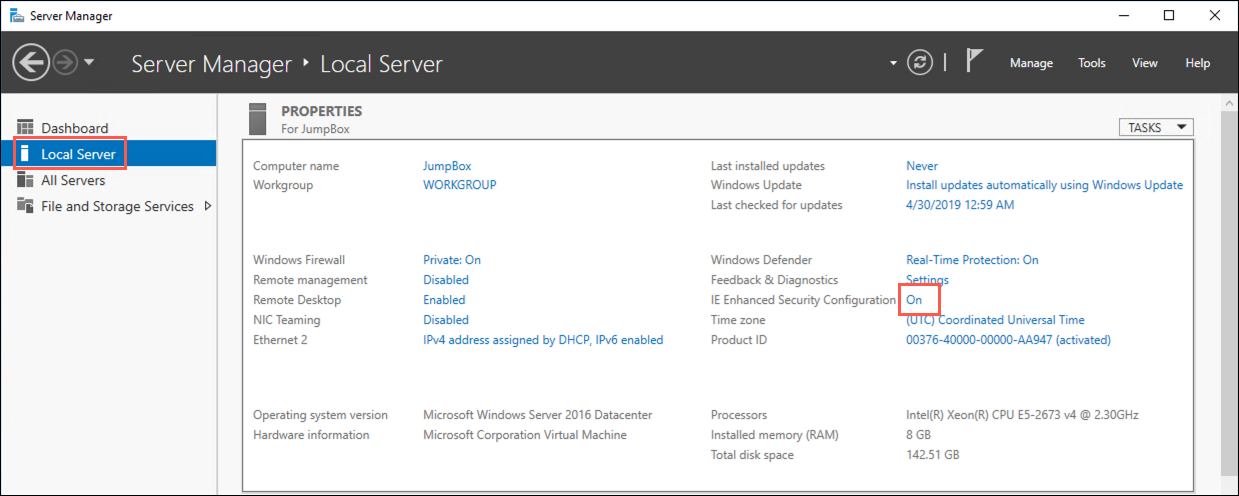
In the Internet Explorer Enhanced Security Configuration dialog, select Off under both Administrators and Users, and then select OK.
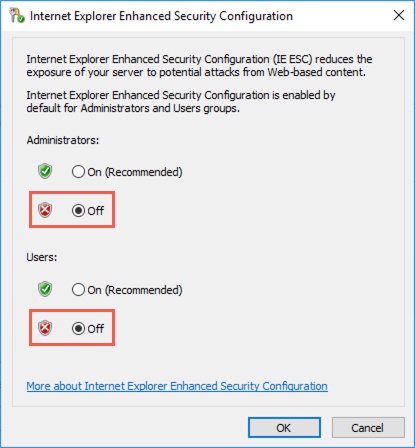
You can close the Server Manager but leave the connection to the LabVM open for the next task.
In this task, you configure the LabVM with the required software and downloads. First, you download and install the Microsoft Edge web browser. Next, you download a copy of the Visual Studio starter solution and unzip it into a folder named C:\ServerlessMCW.
Note: Some aspects of this lab require using the new Microsoft Edge (Chromium edition) browser. You may find yourself blocked if using Internet Explorer later in the lab, as Internet Explorer is not supported for some specific activities.
To install Microsoft Edge, launch Internet Explorer on the VM and download Microsoft Edge.
Run the downloaded installer and follow the setup instruction.
Next, download a copy of the Serverless Architecture MCW GitHub repo.
Extract the download ZIP file to C:\ServerlessMCW.
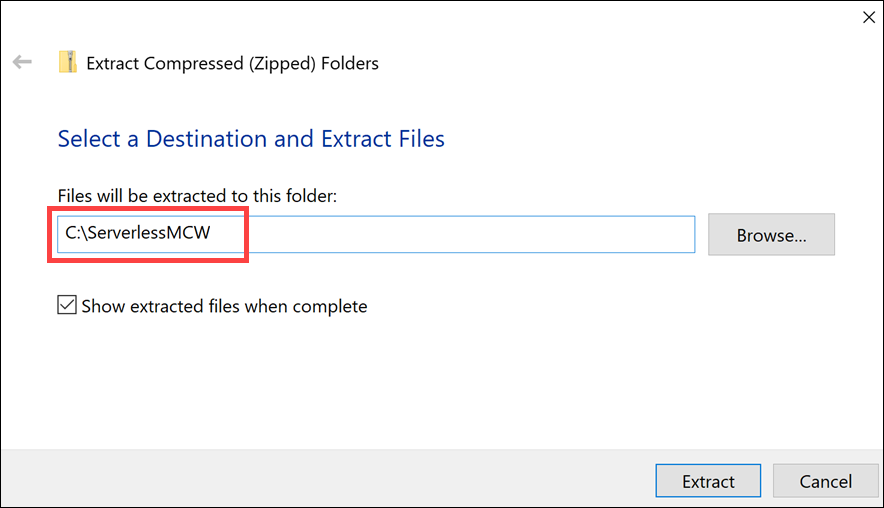
C:\ServerlessMCW entered into the extraction location.